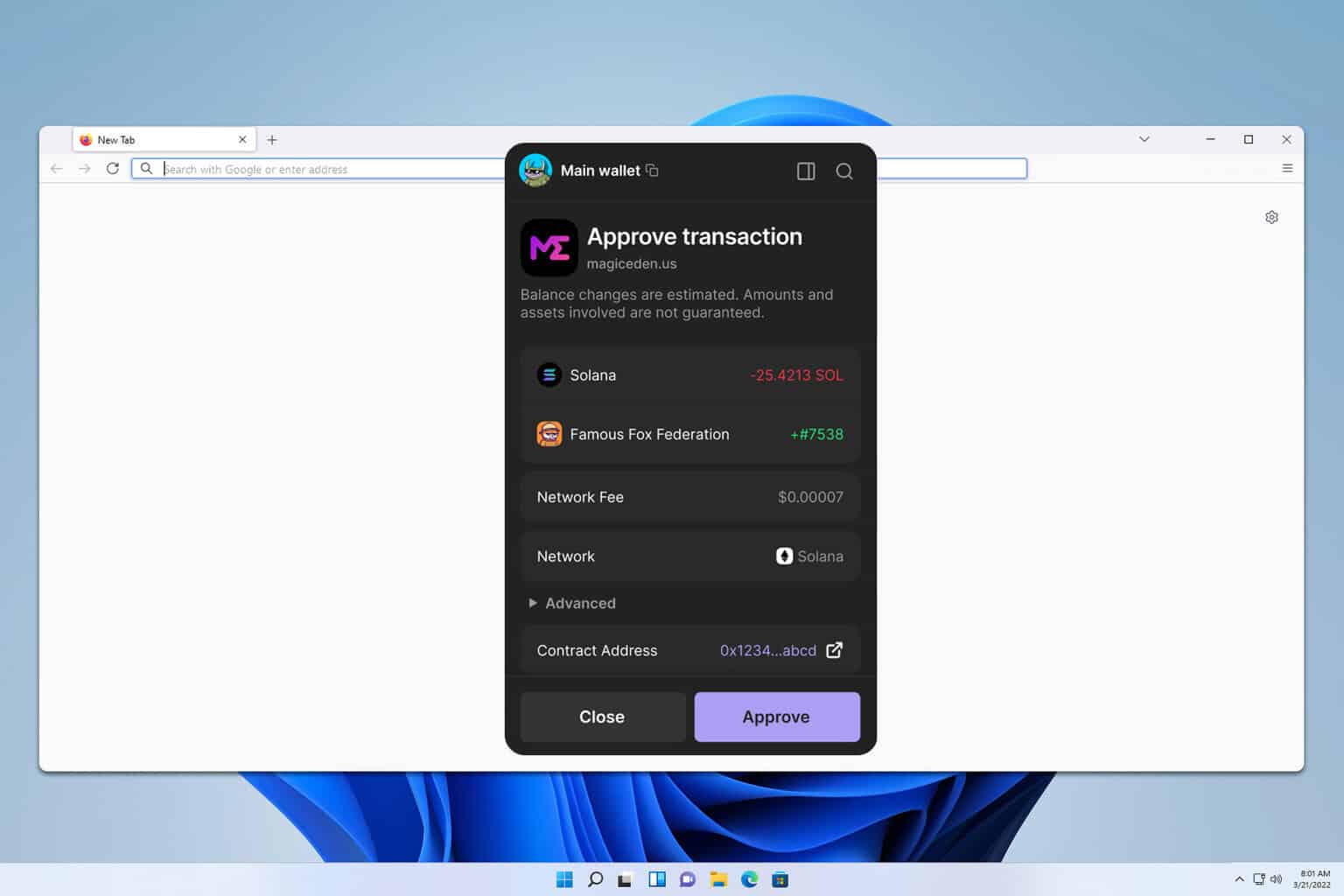
Halfway through a messy token swap on a crowded DEX, I realized my approval pop-up didn’t look right. Whoa! My instinct said “don’t approve” even before I read the fine print. Initially I thought it was just UI noise, but then I checked the contract address and saw somethin’ off—very very important detail that saved me a headache. On one hand Phantom’s UX makes DeFi feel effortless; on the other hand the browser-extension surface invites risk if you relax too much. Hmm… here’s the thing. You can move fast with Solana, and that speed is thrilling, though actually the tradeoff is you must be extra careful about what you sign.
I started using Phantom because it made wallet management feel normal—accounts, tokens, NFTs, quick swaps—simple. Really? Yes. The extension integrates into Chrome and Chromium-based browsers with the kind of polish you’d expect from a consumer app, which is both its strength and its vulnerability. My fast reaction system (System 1) loves the convenience. My slow thinking (System 2) keeps poking holes in each approval workflow, checking balances, cross-referencing transaction data. Initially I trusted the default settings, but then realized that a few small tweaks—pinning the extension, enabling hardware-wallet support—change your threat model a lot.
Setup is straightforward. Short sentence. You create a seed, write it down (like seriously, write it down), and set a password for local encryption. Then you can add multiple accounts, import keys, or connect a Ledger. But don’t blur the lines between convenience and security. On one hand importing a key makes moving tokens easy; though actually, importing means that your private key is stored in the extension and thus exposed to browser-level attacks. So, use hardware wallet attachments for larger balances. And check every “sign” dialog—not just the amount, but the program IDs and fees—because some malicious dApps will ask to approve ridiculous authority scopes that let them drain tokens later.
Permissions in browser extensions are a weird gray area. Wow! Some users click “allow” without thinking. This part bugs me. Extensions can request broad permissions, and browsers grant them at install time. (Oh, and by the way…) Phantom’s legitimate permissions are narrower than many clones, but attackers will spin up lookalike extensions with nearly identical UI and slightly different publisher details. My instinct said to verify the extension carefully the first time I installed it. Actually, wait—let me rephrase that: verify every time you update it, because malicious updates are a known vector.
Where to get Phantom (and a caution)
Okay, so check this out—download links matter. If you ever need a quick link to an installer or mirror for testing, use a single, trusted source and verify the origin. I sometimes use community mirrors to test UX locally, but for real funds I rely only on official channels or hardware confirmations. If you’re exploring a download right now, here’s a link I referenced during testing: https://sites.google.com/cryptowalletextensionus.com/phantomwalletdownloadextension/ and yes, you should double-check the extension’s publisher name, review timestamps, and any cryptographic signatures before trusting it. Seriously—double-check. A neat trick is to search for changelog entries or release notes and match them to the browser store’s version number.
One more practical tip: pin Phantom to your toolbar so fake pop-ups are less likely to trick you. Short. That small visual anchor reduces the chance you’ll click a random floating window. When connecting a dApp, don’t just look at the dApp name—open its site, check social accounts, and if something smells off, back out. My brain still jerks when I see a suspicious domain; I trust that reflex. On the technical side, review the “program ID” that the transaction interacts with—if it’s not a recognized marketplace or staking program, hold up and investigate.
For custodial trade-offs: if you want frictionless swaps, Phantom’s built-in swap is convenient. For privacy, though, the extension stores some local metadata—recent RPC endpoints, token lists you’ve interacted with—so use a trusted RPC or run your own if you care about leaking activity patterns. Initially I thought default RPC endpoints were fine, but then realized network congestion can route you through nodes that may log requests. On one hand most users won’t need a personal node; on the other hand power users should consider it for privacy and reliability.
Phantom supports hardware wallets like Ledger. Wow! Hardware integration is the single biggest step up you can take. It reduces attack surface dramatically because approvals require physical confirmation on the device. I’m biased, but if you hold more than pocket-change, get a hardware wallet and connect it. Also, store your recovery seed offline and never type it into websites. My cautionary tale: someone I knew (not me) once imported a seed into a new device without verifying source—she lost funds after installing a malicious browser extension later. That stuck with me. Don’t be that person.
Transaction hygiene matters. Short. Read transaction payloads. Compare the SOL fee to expected norms. Watch for “Approve all” scopes—some legitimate marketplaces request broad approvals for batch listings, but a blanket approval for “transfer authority for all tokens” is often unnecessary. If a dApp asks for full access to token accounts, decline and ask support why. If they insist without good reason, bail. These are gray areas where trust and verification intersect.
From an engineering perspective, Phantom’s architecture leans on client-side signing and secure local storage. That makes it fast and friendly. But it also means your browser environment matters—extensions, malicious scripts, even compromised OS accounts can be vectors. Keep your OS updated, use ad-blockers to reduce malicious injected scripts, and keep the number of installed extensions minimal. I try to keep only essential extensions active and remove anything I haven’t used in months. Sounds obvious, but people accumulate extensions like browser souvenirs.
FAQ — Quick hits
Is Phantom free to use?
Yes. Short. Phantom does not charge for basic use beyond standard blockchain fees. Fees come from the network and any integrated swap liquidity providers. Be aware of gas and slippage settings during swaps.
How do I verify an extension is the real Phantom?
Check the publisher name, number of downloads, recent reviews, and the exact version number in the Chrome or Edge store—then compare to Phantom’s official channels if possible. Also look for hardware-wallet support and the expected UI. If somethin’ doesn’t line up, don’t install it.
What if I lose my seed phrase?
Recovering without the seed is usually impossible. Short. If you lose access, try any backups you made, cloud vaults only if encrypted and trusted, or hardware-wallet backups. If all else fails, there’s no bailout—so protect the phrase like a physical safe.
Okay—closing thought. I still use Phantom daily. It’s fast, integrates well with Solana dApps, and the team iterates quickly. But convenience breeds complacency. So, adopt small rituals: verify before approving, use a Ledger for large sums, and be skeptical of anything that looks like a shortcut. I’m not 100% sure we’ll solve all UX-vs-security tradeoffs, but until then stay curious and careful. Try it, enjoy the speed, and keep your head about you—this space moves fast and mistakes can be costly…

